How To Set Up Hamachi Vpn
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data beyond shared or public networks as if their computing devices were directly continued to the private network.[1] The benefits of a VPN include increases in functionality, security, and management of the individual network. Information technology provides access to resource that are inaccessible on the public network and is typically used for remote workers. Encryption is common, although not an inherent part of a VPN connexion.[2]
A VPN is created by establishing a virtual point-to-point connexion through the use of dedicated circuits or with tunneling protocols over existing networks. A VPN available from the public Internet can provide some of the benefits of a wide area network (WAN). From a user perspective, the resources available within the individual network can exist accessed remotely.[iii]
Types [edit]

VPN nomenclature tree based on the topology first, then on the technology used.

VPN connectivity overview, showing intranet site-to-site and remote-work configurations used together
Virtual private networks may be classified by several categories:
- Remote access
- A host-to-network configuration is analogous to connecting a computer to a local expanse network. This type provides admission to an enterprise network, such as an intranet. This may be employed for remote workers who need admission to private resources, or to enable a mobile worker to access of import tools without exposing them to the public Internet.
- Site-to-site
- A site-to-site configuration connects two networks. This configuration expands a network across geographically disparate offices, or a group of offices to a data centre installation. The interconnecting link may run over a dissimilar intermediate network, such as two IPv6 networks connected over an IPv4 network.[four]
- Extranet-based site-to-site
- In the context of site-to-site configurations, the terms intranet and extranet are used to describe ii dissimilar use cases.[v] An intranet site-to-site VPN describes a configuration where the sites continued by the VPN belong to the same system, whereas an extranet site-to-site VPN joins sites belonging to multiple organizations.
Typically, individuals interact with remote access VPNs, whereas businesses tend to make use of site-to-site connections for business-to-business organisation, cloud computing, and co-operative function scenarios. Despite this, these technologies are not mutually exclusive and, in a significantly circuitous business concern network, may be combined to enable remote access to resources located at any given site, such equally an ordering arrangement that resides in a datacenter.
VPN systems also may be classified by:
- the tunneling protocol used to tunnel the traffic
- the tunnel'south termination point location, eastward.g., on the customer border or network-provider edge
- the type of topology of connections, such equally site-to-site or network-to-network
- the levels of security provided
- the OSI layer they nowadays to the connecting network, such as Layer 2 circuits or Layer 3 network connectivity
- the number of simultaneous connections
Security mechanisms [edit]
VPNs cannot make online connections completely anonymous, but they can usually increase privacy and security. To prevent disclosure of private information, VPNs typically permit but authenticated remote access using tunneling protocols and encryption techniques.
The VPN security model provides:
- confidentiality such that even if the network traffic is sniffed at the packet level (see network sniffer and deep packet inspection), an assailant would see merely encrypted information
- sender authentication to prevent unauthorized users from accessing the VPN
- bulletin integrity to detect whatever instances of tampering with transmitted messages.
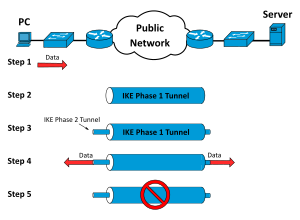
The life bike phases of an IPSec Tunnel in a virtual private network.
Secure VPN protocols include the following:
- Internet Protocol Security (IPsec) was initially adult by the Internet Engineering Task Force (IETF) for IPv6, which was required in all standards-compliant implementations of IPv6 before RFC 6434 fabricated it only a recommendation.[6] This standards-based security protocol is also widely used with IPv4 and the Layer 2 Tunneling Protocol. Its design meets most security goals: availability, integrity, and confidentiality. IPsec uses encryption, encapsulating an IP parcel inside an IPsec package. De-encapsulation happens at the cease of the tunnel, where the original IP packet is decrypted and forwarded to its intended destination.
- Ship Layer Security (SSL/TLS) can tunnel an entire network'south traffic (as it does in the OpenVPN project and SoftEther VPN project[7]) or secure an individual connectedness. A number of vendors provide remote-admission VPN capabilities through SSL. An SSL VPN tin can connect from locations where IPsec runs into problem with Network Address Translation and firewall rules.
- Datagram Transport Layer Security (DTLS) – used in Cisco AnyConnect VPN and in OpenConnect VPN[8] to solve the issues SSL/TLS has with tunneling over TCP (tunneling TCP over TCP tin can pb to big delays and connexion aborts[9]).
- Microsoft Point-to-Point Encryption (MPPE) works with the Point-to-Point Tunneling Protocol and in several compatible implementations on other platforms.
- Microsoft Secure Socket Tunneling Protocol (SSTP) tunnels Indicate-to-Point Protocol (PPP) or Layer 2 Tunneling Protocol traffic through an SSL/TLS channel (SSTP was introduced in Windows Server 2008 and in Windows Vista Service Pack 1).
- Multi Path Virtual Private Network (MPVPN). Ragula Systems Evolution Company owns the registered trademark "MPVPN".[10]
- Secure Shell (SSH) VPN – OpenSSH offers VPN tunneling (singled-out from port forwarding) to secure remote connections to a network or to inter-network links. OpenSSH server provides a limited number of concurrent tunnels. The VPN feature itself does non support personal authentication.[xi] [12] [thirteen]
- WireGuard is a protocol. In 2022, WireGuard support was added to both the Linux[fourteen] and Android[15] kernels, opening it upwards to adoption by VPN providers. By default, WireGuard utilizes Curve25519 for key exchange and ChaCha20 for encryption, just also includes the ability to pre-share a symmetric key between the client and server.[sixteen] [17]
- IKEv2 is an acronym that stands for Internet Key Commutation volume two. It was created by Microsoft and Cisco and is used in conjunction with IPSec for encryption and authentication. Its primary use is in mobile devices, whether on 3G or 4G LTE networks, since it is effective at rejoining when a connectedness is lost.
Authentication [edit]
Tunnel endpoints must be authenticated before secure VPN tunnels can exist established. User-created remote-access VPNs may utilize passwords, biometrics, two-factor authentication or other cryptographic methods. Network-to-network tunnels ofttimes use passwords or digital certificates. They permanently store the cardinal to permit the tunnel to constitute automatically, without intervention from the administrator.
Routing [edit]
Tunneling protocols tin can operate in a point-to-point network topology that would theoretically non be considered a VPN because a VPN by definition is expected to support arbitrary and changing sets of network nodes. Only since most router implementations support a software-defined tunnel interface, customer-provisioned VPNs often are simply divers tunnels running conventional routing protocols.
Provider-provisioned VPN building-blocks [edit]

Site-to-Site VPN terminology.
Depending on whether a provider-provisioned VPN (PPVPN) operates in Layer ii (L2) or Layer three (L3), the building blocks described below may exist L2 only, L3 only, or a combination of both. Multi-protocol characterization switching (MPLS) functionality blurs the L2-L3 identity.[18] [ original enquiry? ]
RFC 4026 generalized the following terms to comprehend L2 MPLS VPNs and L3 (BGP) VPNs, but they were introduced in RFC 2547.[19] [twenty]
- Client (C) devices
A device that is within a client's network and not directly connected to the service provider'south network. C devices are not enlightened of the VPN.
- Client Edge device (CE)
A device at the edge of the client'southward network which provides access to the PPVPN. Sometimes it is merely a demarcation point between provider and customer responsibleness. Other providers allow customers to configure information technology.
- Provider edge device (PE)
A device, or set of devices, at the border of the provider network which connects to customer networks through CE devices and presents the provider's view of the customer site. Pes are enlightened of the VPNs that connect through them, and maintain VPN land.
- Provider device (P)
A device that operates inside the provider's core network and does not directly interface to whatsoever client endpoint. It might, for example, provide routing for many provider-operated tunnels that belong to unlike customers' PPVPNs. While the P device is a key part of implementing PPVPNs, information technology is not itself VPN-enlightened and does not maintain VPN state. Its primary role is allowing the service provider to scale its PPVPN offerings, for instance, by acting equally an assemblage betoken for multiple PEs. P-to-P connections, in such a role, often are loftier-capacity optical links between major locations of providers.
User-visible PPVPN services [edit]
OSI Layer 2 services [edit]
- Virtual LAN
Virtual LAN (VLAN) is a Layer 2 technique that allows for the coexistence of multiple local area network (LAN) circulate domains interconnected via trunks using the IEEE 802.1Q trunking protocol. Other trunking protocols have been used but have become obsolete, including Inter-Switch Link (ISL), IEEE 802.10 (originally a security protocol but a subset was introduced for trunking), and ATM LAN Emulation (LANE).
- Virtual private LAN service (VPLS)
Developed by Institute of Electric and Electronics Engineers, Virtual LANs (VLANs) allow multiple tagged LANs to share common trunking. VLANs frequently comprise only customer-owned facilities. Whereas VPLS as described in the to a higher place section (OSI Layer 1 services) supports emulation of both point-to-point and point-to-multipoint topologies, the method discussed here extends Layer 2 technologies such equally 802.1d and 802.1q LAN trunking to run over transports such as Metro Ethernet.
As used in this context, a VPLS is a Layer 2 PPVPN, emulating the full functionality of a traditional LAN. From a user standpoint, a VPLS makes it possible to interconnect several LAN segments over a packet-switched, or optical, provider core, a cadre transparent to the user, making the remote LAN segments behave as one single LAN.[21]
In a VPLS, the provider network emulates a learning bridge, which optionally may include VLAN service.
- Pseudo wire (PW)
Pow is like to VPLS, but it tin provide different L2 protocols at both ends. Typically, its interface is a WAN protocol such as Asynchronous Transfer Mode or Frame Relay. In contrast, when aiming to provide the appearance of a LAN contiguous betwixt two or more locations, the Virtual Private LAN service or IPLS would be appropriate.
- Ethernet over IP tunneling
EtherIP (RFC 3378)[22] is an Ethernet over IP tunneling protocol specification. EtherIP has only bundle encapsulation mechanism. It has no confidentiality nor message integrity protection. EtherIP was introduced in the FreeBSD network stack[23] and the SoftEther VPN[24] server program.
- IP-only LAN-similar service (IPLS)
A subset of VPLS, the CE devices must accept Layer 3 capabilities; the IPLS presents packets rather than frames. It may support IPv4 or IPv6.
OSI Layer 3 PPVPN architectures [edit]
This section discusses the main architectures for PPVPNs, one where the PE disambiguates indistinguishable addresses in a unmarried routing instance, and the other, virtual router, in which the PE contains a virtual router instance per VPN. The onetime approach, and its variants, accept gained the nigh attention.
One of the challenges of PPVPNs involves different customers using the same address space, especially the IPv4 private address infinite.[25] The provider must be able to disambiguate overlapping addresses in the multiple customers' PPVPNs.
- BGP/MPLS PPVPN
In the method defined by RFC 2547, BGP extensions advertise routes in the IPv4 VPN accost family, which are of the form of 12-byte strings, beginning with an viii-byte route distinguisher (RD) and ending with a 4-byte IPv4 accost. RDs disambiguate otherwise indistinguishable addresses in the aforementioned PE.
PEs empathize the topology of each VPN, which are interconnected with MPLS tunnels either directly or via P routers. In MPLS terminology, the P routers are label switch routers without awareness of VPNs.
- Virtual router PPVPN
The virtual router compages,[26] [27] every bit opposed to BGP/MPLS techniques, requires no modification to existing routing protocols such as BGP. By the provisioning of logically independent routing domains, the customer operating a VPN is completely responsible for the address space. In the various MPLS tunnels, the unlike PPVPNs are disambiguated by their characterization but do not need routing distinguishers.
Unencrypted tunnels [edit]
Some virtual networks use tunneling protocols without encryption for protecting the privacy of data. While VPNs frequently practise provide security, an unencrypted overlay network does not neatly fit within the secure or trusted categorization.[28] For instance, a tunnel set upwards between two hosts with Generic Routing Encapsulation (GRE) is a virtual individual network just is neither secure nor trusted.[29] [thirty]
Native plaintext tunneling protocols include Layer 2 Tunneling Protocol (L2TP) when information technology is prepare without IPsec and Point-to-Point Tunneling Protocol (PPTP) or Microsoft Betoken-to-Point Encryption (MPPE).[31]
Trusted delivery networks [edit]
Trusted VPNs do not use cryptographic tunneling; instead they rely on the security of a unmarried provider'due south network to protect the traffic.[32]
- Multi-Protocol Label Switching (MPLS) often overlays VPNs, frequently with quality-of-service control over a trusted delivery network.
- L2TP[33] which is a standards-based replacement, and a compromise taking the good features from each, for two proprietary VPN protocols: Cisco'south Layer 2 Forwarding (L2F)[34] (obsolete as of 2009[update]) and Microsoft'due south Point-to-Point Tunneling Protocol (PPTP).[35]
From the security standpoint, VPNs either trust the underlying delivery network or must enforce security with mechanisms in the VPN itself. Unless the trusted delivery network runs amid physically secure sites just, both trusted and secure models need an authentication mechanism for users to gain access to the VPN.
VPNs in mobile environments [edit]
Mobile virtual private networks are used in settings where an endpoint of the VPN is not stock-still to a unmarried IP address, merely instead roams across various networks such equally data networks from cellular carriers or betwixt multiple Wi-Fi access points without dropping the secure VPN session or losing application sessions.[36] Mobile VPNs are widely used in public safety where they give law-enforcement officers admission to applications such as computer-assisted dispatch and criminal databases,[37] and in other organizations with like requirements such equally field service management and healthcare.[38] [ need quotation to verify ].
Networking limitations [edit]
A limitation of traditional VPNs is that they are point-to-signal connections and do non tend to support circulate domains; therefore, communication, software, and networking, which are based on layer two and circulate packets, such as NetBIOS used in Windows networking, may not be fully supported as on a local area network. Variants on VPN such as Virtual Private LAN Service (VPLS) and layer 2 tunneling protocols are designed to overcome this limitation.[39]
Common misconceptions [edit]
- A VPN does not brand your internet "individual". You can still be tracked through tracking cookies and device fingerprinting, fifty-fifty if your IP address is hidden.[forty]
- A VPN does not make you allowed to hackers.[forty]
Meet likewise [edit]
- Anonymizer
- Dynamic Multipoint Virtual Individual Network
- Ethernet VPN
- Internet privacy
- Mediated VPN
- Opportunistic encryption
- Split tunneling
- Virtual private server
- VPN service
References [edit]
- ^ "What Is a VPN? - Virtual Individual Network". Cisco . Retrieved 5 September 2022.
- ^ Mason, Andrew G. (2002). Cisco Secure Virtual Private Network . Cisco Press. p. 7. ISBN9781587050336.
- ^ "Virtual Private Networking: An Overview". TechNet. Microsoft Docs. iv September 2001. Retrieved 7 November 2022.
- ^ Davies, Joseph (July 2007). "IPv6 Traffic over VPN Connections". The Cable Guy. TechNet Magazine . Retrieved 7 Nov 2022 – via Microsoft Docs.
- ^ RFC 3809 - Generic Requirements for Provider Provisioned Virtual Individual Networks. sec. 1.1. doi:x.17487/RFC3809. RFC 3809.
- ^ RFC 6434, "IPv6 Node Requirements", East. Jankiewicz, J. Loughney, T. Narten (December 2022)
- ^ "one. Ultimate Powerful VPN Connectivity". world wide web.softether.org. SoftEther VPN Project.
- ^ "OpenConnect". Retrieved 8 April 2022.
OpenConnect is a customer for Cisco'due south AnyConnect SSL VPN [...] OpenConnect is not officially supported by, or associated in whatever way with, Cisco Systems. It merely happens to interoperate with their equipment.
- ^ "Why TCP Over TCP Is A Bad Thought". sites.inka.de . Retrieved 24 October 2022.
- ^ "Trademark Status & Document Retrieval". tarr.uspto.gov.
- ^ "ssh(i) – OpenBSD transmission pages". man.openbsd.org.
- ^ c@cb.vu, Colin Barschel. "Unix Toolbox". cb.vu.
- ^ "SSH_VPN – Community Help Wiki". aid.ubuntu.com.
- ^ Salter, Jim (30 March 2022). "WireGuard VPN makes it to 1.0.0—and into the next Linux kernel". Ars Technica . Retrieved thirty June 2022.
- ^ "Diff - 99761f1eac33d14a4b1613ae4b7076f41cb2df94^! - kernel/common - Git at Google". android.googlesource.com . Retrieved 30 June 2022.
- ^ Younglove, R. (Dec 2000). "Virtual private networks - how they work". Computing & Command Engineering Journal. 11 (six): 260–262. doi:10.1049/cce:20000602. ISSN 0956-3385.
- ^ Benjamin Dowling, and Kenneth G. Paterson (12 June 2022). "A cryptographic analysis of the WireGuard protocol". International Conference on Applied Cryptography and Network Security. ISBN978-iii-319-93386-3.
- ^ "Configuring PFC3BXL and PFC3B Mode Multiprotocol Characterization Switching" (PDF).
- ^ E. Rosen & Y. Rekhter (March 1999). "BGP/MPLS VPNs". Internet Engineering Task Strength (IETF). RFC2547.
- ^ Lewis, Marking (2006). Comparing, designing, and deploying VPNs (1st print. ed.). Indianapolis, Ind.: Cisco Press. pp. 5–6. ISBN1587051796.
- ^ Ethernet Bridging (OpenVPN)
- ^ Hollenbeck, Scott; Housley, Russell. "EtherIP: Tunneling Ethernet Frames in IP Datagrams".
- ^ Glyn M Burton: RFC 3378 EtherIP with FreeBSD, 03 February 2022
- ^ net-security.org news: Multi-protocol SoftEther VPN becomes open up source, January 2022
- ^ Address Allocation for Private Internets, RFC 1918, Y. Rekhter et al., February 1996
- ^ RFC 2917, A Cadre MPLS IP VPN Architecture
- ^ RFC 2918, Eastward. Chen (September 2000)
- ^ Yang, Yanyan (2006). "IPsec/VPN security policy correctness and assurance". Periodical of High Speed Networks. 15: 275–289. CiteSeerX10.1.1.94.8561.
- ^ "Overview of Provider Provisioned Virtual Individual Networks (PPVPN)". Secure Thoughts. Retrieved 29 August 2022.
- ^ RFC 1702: Generic Routing Encapsulation over IPv4 networks. October 1994.
- ^ IETF (1999), RFC 2661, Layer 2 Tunneling Protocol "L2TP"
- ^ Cisco Systems, Inc. (2004). Internetworking Technologies Handbook. Networking Technology Series (4 ed.). Cisco Press. p. 233. ISBN9781587051197 . Retrieved 15 February 2022.
[...] VPNs using dedicated circuits, such equally Frame Relay [...] are sometimes called trusted VPNsouth, considering customers trust that the network facilities operated by the service providers volition not be compromised.
- ^ Layer Two Tunneling Protocol "L2TP", RFC 2661, W. Townsley et al., August 1999
- ^ IP Based Virtual Private Networks, RFC 2341, A. Valencia et al., May 1998
- ^ Point-to-Point Tunneling Protocol (PPTP), RFC 2637, M. Hamzeh et al., July 1999
- ^ Phifer, Lisa. "Mobile VPN: Endmost the Gap", SearchMobileComputing.com, July xvi, 2006.
- ^ Willett, Andy. "Solving the Calculating Challenges of Mobile Officers", www.officer.com, May, 2006.
- ^ Cheng, Roger. "Lost Connections", The Wall Street Journal, December 11, 2007.
- ^ Sowells, Julia (seven August 2022). "Virtual Private Network (VPN) : What VPN Is And How Information technology Works". Hackercombat . Retrieved 7 Nov 2022.
- ^ a b O'sullivan, Fergus. "VPN Myths Debunked: What VPNs Tin and Cannot Do". How-To Geek . Retrieved xvi January 2022.
Further reading [edit]
- Kelly, Sean (Baronial 2001). "Necessity is the mother of VPN invention". Advice News: 26–28. ISSN 0010-3632. Archived from the original on 17 December 2001.
How To Set Up Hamachi Vpn,
Source: https://en.wikipedia.org/wiki/Virtual_private_network
Posted by: mcculloughpornat1956.blogspot.com


0 Response to "How To Set Up Hamachi Vpn"
Post a Comment